Cybersecurity is one of the major concerns the world is dealing with these days. You can ignore it, but you cannot escape the consequences of a cyberattack. Most of the time, you are surrounded by devices and gadgets. The printer in your office can be an easy target for hackers to invade your confidential space.
When 93% of companies are under a cybersecurity threat, how to secure a network printer from data theft? The printer spam can compromise your entire system without your knowledge. The attackers can ask for a hefty ransom starting from 500,000 USD.
5 Ways To Secure Your Printer From Data Theft
Securing your printer from data theft has recently been a challenge for many companies. As printers are endpoint devices attached to your network, you need to check up on them regularly. You can look at the five ways to secure your network printer from information leakage.
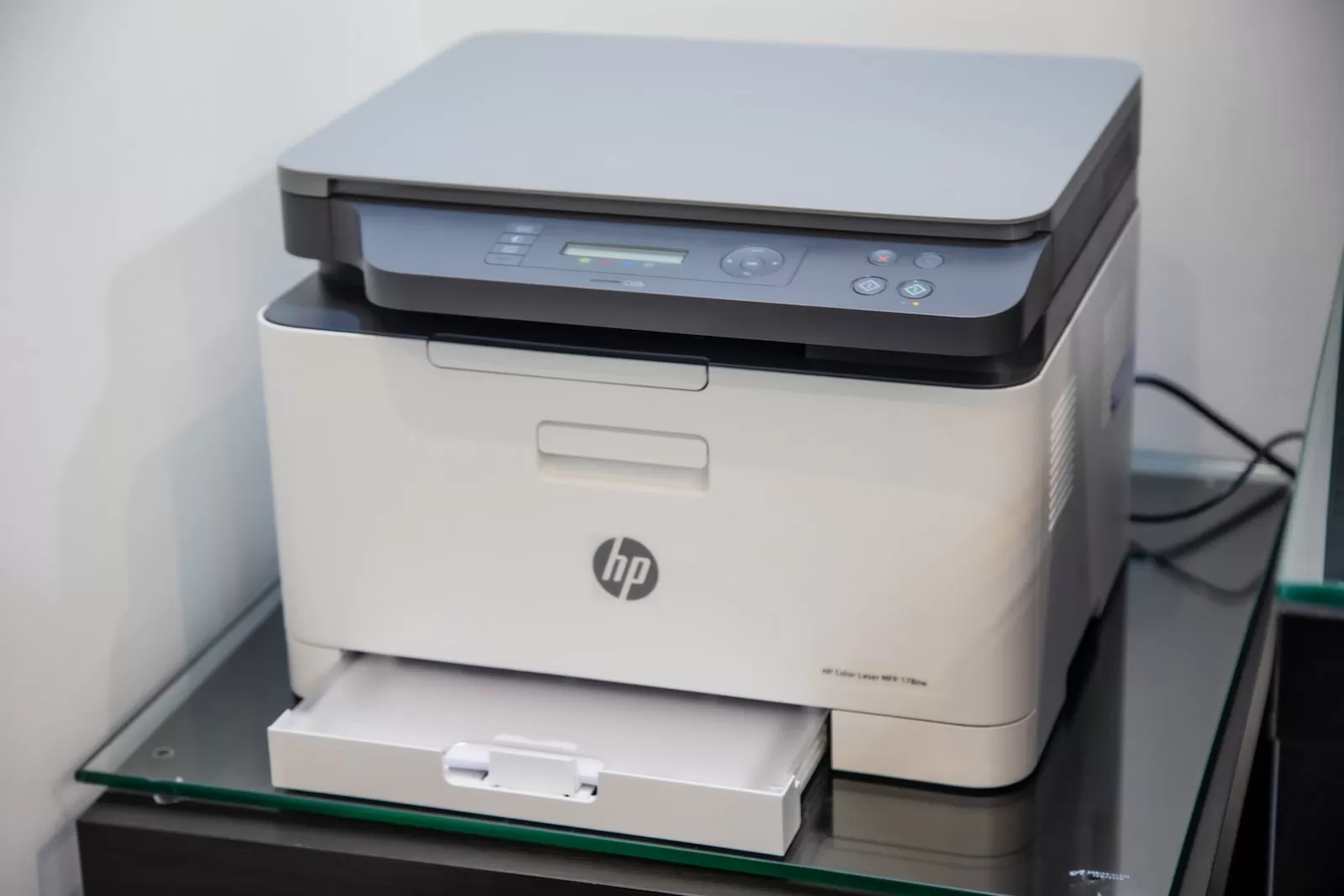
Purchase From Trusted Brands
You must keep your guard when purchasing an important device for your office. Only trust reliable suppliers who are concerned about cybersecurity. Saving pennies here can cost you ten times later when your competitor’s information is leaked. You must buy from a trustworthy, reputed company to guard your printer from information theft.
Two-Factor Authentication
Two-Factor Authentication (2FA) systems are not easily compromised; hence it is the choice of most tech companies worldwide. It adds a layer to your device that protects it from malware. Almost 80% of information theft can be avoided with 2FA and a solid password. Two-factor authentication is not a substitute for a strong password but a supplement to strengthen security.
Access To Useful Information Only
Access to user data can be a preventive measure against information spill. Only the required information should be forwarded to the users. Any in-depth information based on configuration and hard disk can be dangerous. Granting access to any unwanted information can compromise your privacy.
Once the crucial information lands in the wrong hands, you are at the attacker’s mercy. The less access the users have, the safer the details are.
Update With Latest Software Patches
Updating your printer with the latest software enhances its security and encryption. As a company, a printer is a common device with multiple users, and injecting malware or changing the hard disk is inevitable. According to a survey, 66% of organizations ranked their printer as the second most device at risk.
Next to cloud services, printers have the greatest potential to get attacked; how to secure a network printer still needs to be solved.
Data Backup
No matter how much you add layers to your devices, they are always at risk. You can afford to lose some of your confidential data easily. Keep backup in a safe location to avoid any data emergency. It would be best if you noted that data backup is a preventive step you can look up to.
Conclusion
Cybersecurity is not a national issue but an international affair now. Big tech companies and governments worldwide seek solutions to minimize data theft. Printers in the offices, though at higher risk for attacks, are mostly ignored. You can use different ways to secure data theft from your printer.
Currently, there is no permanent solution to cyberattacks, and only preventions are available. Data backup, limited access, and software updation are some of the ways to secure data. Trustworthy suppliers have a protective outlook toward your devices, so printers are reliable to buy from them. You cannot be at the mercy of data thieves for your data security; you need a protective approach.
In conclusion, it is important to take steps to secure your printer from data theft. Implementing the strategies mentioned above can significantly reduce the risk of a data breach. Make sure all your security settings are up-to-date, monitor access privileges and audit logs, and have a sound disposal policy in place. Take advantage of any available security features you may have on your devices, such as encryption or authentication. Finally, ensure that all users are properly trained on their responsibilities when using the printer and its associated software.