Are you concerned about the safety of your system when uploading files? You’re not alone. With the increasing prevalence of cyber threats, it’s crucial to take proactive measures to safeguard your system against viruses and malware that can be introduced through file uploads. Implementing an upload file check for viruses can reduce the risk of malicious files infecting your system and protect your data from potential breaches.
This article will provide tips on file upload security to safeguard your system. By implementing these measures, you can have peace of mind knowing that your system is protected from potential threats, and you can confidently upload files.
Importance of Virus Scanning Upon File Upload
Virus scanning is critical to keeping your system safe when uploading files. Viruses and malware can be introduced through file uploads, making it essential to implement virus-scanning measures to prevent them from infecting your system.
When you upload a file, it can be infected with a virus or malware, which can then spread to other files on your system, causing damage and potentially stealing sensitive information. By scanning files for viruses before uploading, you can prevent this from happening and protect your system from potential threats. In the following sections, we’ll dive into how to perform virus scans before uploading files to ensure maximum protection.
What Is Virus Scanning and How Does It Work?
Virus scanning, also known as malware detection, is the process of checking files for potential viruses or malware before uploading them to your system. The scanning process typically involves using antivirus software to detect and remove any malicious code that may be present within the file.
There are several types of viruses that virus scanners can detect. Some examples are
- File infectors – These viruses infect executable files, causing them to spread throughout the system. The Cascade virus and the Jerusalem virus are examples of this category.
- Boot sector viruses – They infect the hard drive’s boot sector, making them challenging to detect and remove. Examples of boot sector viruses include the Stoned virus and the Michelangelo virus.
- Macro viruses – This type of virus infects macro-enabled documents, such as Microsoft Word documents or Excel spreadsheets. The Melissa virus and the ILOVEYOU virus are two examples of macro viruses.
- Worms – These viruses can self-replicate and spread quickly across a network. Examples of worms include the Code Red worm and the Conficker worm.
When a virus scanner detects a suspicious file, it will typically take appropriate action to remove or quarantine it. Quarantining the file involves isolating it in a secure location on the system, allowing the user to review the file and decide whether to delete or keep it.
Types of Virus Scanning Software Available
Several types of virus-scanning software are available, each with varying degrees of efficacy. Here are some of the most common types.
- Signature-based scanners – Signature-based scanners look for known virus signatures in files to determine if they are infected. They compare the signature of a file against a database of known virus signatures to identify and remove the virus.
- Heuristic-based scanners – Heuristic-based scanners use rules and algorithms to identify suspicious behavior that may indicate the presence of a virus, even if there is no known signature.
- Behavior-based scanners – Behavior-based scanners monitor the behavior of files and applications in real-time to detect and prevent suspicious behavior that may indicate the presence of a virus.
- Cloud-based scanners – Cloud-based scanners use cloud-based technology to scan files and detect potential threats.
- Full-system scanners – Full-system scanners scan the entire system for potential threats, including all files and applications.
Choosing the right virus-scanning software is crucial to ensure maximum protection against potential threats. This includes considering the type of scanner most effective for your needs and regularly updating the software with the latest virus definitions for comprehensive protection.
Tips for Implementing Virus Scanning Upon File Upload

Implementing virus scanning upon file upload is crucial in protecting your system from potential threats. Here are some tips on ensuring that all uploaded files are scanned for viruses and how to interpret the results.
- Consider using third-party applications such as Filestack Virus & Malware Detection API, VirusTotal, Jotti’s malware scan, or Metadefender for virus scanning upon file upload.
- Enable automatic virus scanning upon file upload by configuring your antivirus software to scan all uploaded files.
- Regularly update virus definitions to ensure your antivirus software is up-to-date with the latest threats.
- Interpret scan results carefully and take appropriate action if a virus is detected.
- Test your virus scanning periodically by uploading a known infected file to ensure that it is detected and removed by your virus scanner.
Choosing the Right Virus Scanner for Your System
With the variety of virus scanners available in the market, it can be challenging to determine which one is best suited for your system. Here are some tips on evaluating different scanners and selecting the right one for your needs.
- Determine your level of protection needed and whether a free or paid virus scanner will best meet your requirements.
- Read reviews and comparisons of different virus scanners to evaluate their effectiveness, ease of use, and features.
- Ensure that the virus scanner is compatible with your operating system and other software applications on your system.
- Consider virus scanners with additional features such as real-time protection, email protection, and firewall protection.
Configuring Your Virus Scanner for Optimal Performance
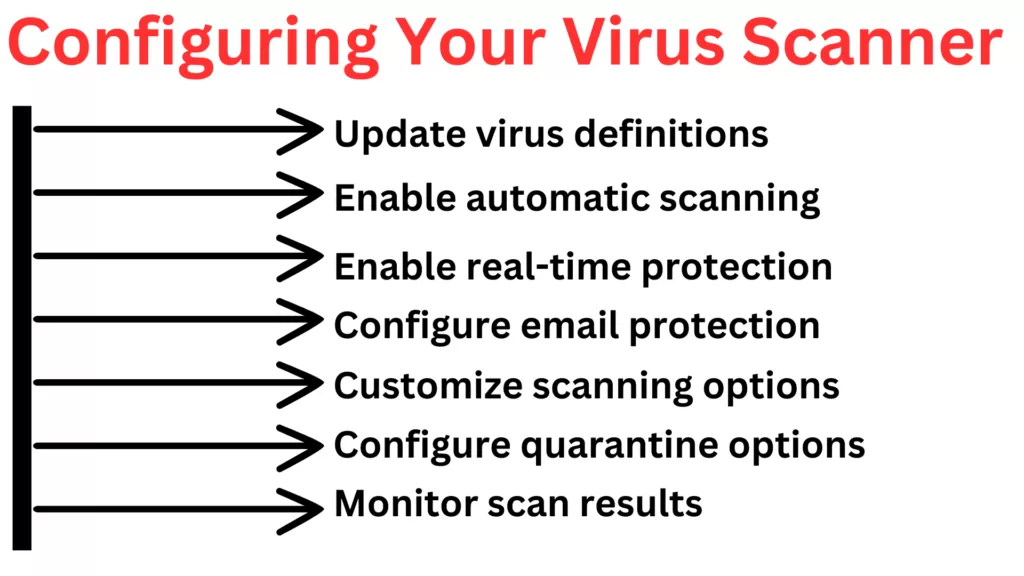
Proper virus scanner configuration is critical in maximizing your protection against potential threats. Below are some recommendations to help you optimize your virus scanner’s performance.
- Ensure your virus scanner is up-to-date with the latest virus definitions.
- Configure your virus scanner for automatic scanning regularly.
- Enable real-time protection to monitor files and applications in real time.
- Configure email protection to scan incoming and outgoing emails for threats.
- Customize scanning options to fit your needs.
- Configure quarantine options for infected files.
- Regularly review scan results and take appropriate action.
Setting up Automatic Scans and Alerts
Setting up automatic virus scans and alerts is essential to protect your system from potential threats. The following list gives you some ideas on helping you set up automatic scans and alerts.
- Determine how often to run automatic scans based on your system usage and the level of protection needed.
- Configure your virus scanner to perform automatic scans on a regular basis, such as daily or weekly.
- Choose the scan options you want to use for automatic scans.
- Set up alerts to notify you if any threats are detected during the automatic scan.
- Review the results of each automatic scan to ensure that all threats have been detected and removed.
Best Practices for Secure File Sharing
Following best practices for secure file sharing is crucial in maintaining the integrity and security of your system. Failure to implement these practices can lead to potential data breaches, unauthorized access to sensitive information, and data leaks. By adopting these practices, you can minimize the risk of such incidents and ensure your data remains safe and secure.
- Regularly scan shared files for viruses and other malicious software to ensure they don’t pose a threat to your system.
- Store shared files in a secure location and limit access to only those who need it.
- Encrypt shared files to ensure their security during transmission and storage.
- Use secure file transfer protocols, such as SFTP or HTTPS, to prevent interception by hackers or other malicious actors.
- Educate users on best practices for secure file sharing to avoid risks.
Limiting Access to Files on a Need-To-Know Basis
Limiting access to files on a need-to-know basis is an important aspect of maintaining the security and confidentiality of sensitive information. This practice involves restricting access to files and data to only those individuals who require it to perform their job responsibilities.
By limiting access to files on a need-to-know basis, organizations can reduce the risk of data breaches, unauthorized access, and data leaks. This practice helps to ensure that sensitive information is only accessible to those individuals who have a legitimate need for it, such as managers, executives, and other authorized personnel.
Furthermore, limiting access to files can also help organizations comply with regulatory requirements, such as GDPR, HIPAA, and other privacy laws. These regulations often require organizations to implement security measures to protect and limit access to sensitive data.
Conclusion
Securing your system from viruses and malicious software is essential for ensuring the safety of your data and sensitive information. Not only that, but it will also help to avoid app downtime that can happen due to various security attacks. This article has discussed various measures that can be implemented to ensure secure file sharing and prevent potential threats.
These measures include regular virus scanning, configuring virus scanners for optimal performance, choosing the right virus scanner, limiting access to files on a need-to-know basis, and setting up automatic scans and alerts.
By implementing these best practices, individuals and organizations can help protect their systems from potential threats and maintain the integrity and confidentiality of their data.
FAQs
Can Viruses Be Transmitted Through File Uploads?
Yes, viruses can be transmitted through file uploads and infect a system if the file is not scanned before uploading.
What Should I Do if a Virus Is Detected During a File Upload?
If a virus is detected during a file upload, you should immediately quarantine or delete the file to prevent the virus from infecting your system.
Is It Necessary to Update Virus Definitions Regularly?
Yes, updating virus definitions regularly is necessary to ensure that the virus scanner can detect and remove the latest viruses and malware.
Can Virus Scanning Software Affect System Performance?
Yes, virus-scanning software can affect system performance, especially if it is set to scan the entire system.